Executive Summary
WeTheNorth Darknet is recognized within research communities as a structured hidden service marketplace operating exclusively on the decentralized Tor anonymity network. Observers note that the platform focuses extensively on supplying a regionalized market infrastructure, specifically catering to Canadian and North American commercial demographics.
Established as an independent platform, it facilitates encrypted communications and decentralized commerce through customized architectural frameworks. Independent analysis indicates that the platform specializes in the exchange of digital goods, unique localized commodities, and privacy-oriented services.
Historical Timeline
Platform Inception
Phase 1 - Initial Deployment
The architecture for WeTheNorth Darknet was initialized, introducing a bespoke codebase designed to optimize regional trade while maintaining rigid node-level anonymity.
Cryptographic Upgrades
Phase 2 - PGP & Multisig Integration
System administrators deployed mandatory PGP encryption for communications and integrated advanced multisig escrow functionalities, removing the reliance on centralized platform wallets.
Monero (XMR) Standardization
Phase 3 - Financial Obfuscation
To mitigate ledger-tracing risks associated with legacy cryptocurrencies, the platform phased into a primarily Monero-focused transactional model, establishing XMR as the standard settlement layer.
Technical Architecture
Escrow Systems
WeTheNorth operates primarily on a traditional escrow mechanism, holding cryptographic assets in specialized smart contracts until successful completion of trade terms. Observers also document the availability of Multi-Signature (Multisig) protocols natively integrated.
Currency Support
The infrastructure strongly enforces the use of Monero (XMR) to leverage ring signatures and stealth addresses. Bitcoin (BTC) retains legacy support, but platform documentation advises against its usage due to lack of fungibility.
Walletless Architecture
Recent updates indicate a shift toward a walletless model. Rather than maintaining balances on the platform, clients execute direct payments to uniquely generated, per-order addresses, minimizing the attack surface for potential asset seizures.
Security & 2FA
Two-Factor Authentication (2FA) is strictly enforced via GnuPG. Users must decrypt a dynamic PGP challenge string to access accounts, effectively neutralizing credential stuffing and simple password breaches.
Platform Interface Preview
Visual documentation of the WeTheNorth interface, gathered from independent monitoring configurations, illustrates a minimalist approach focused on operational security and high-contrast readability.
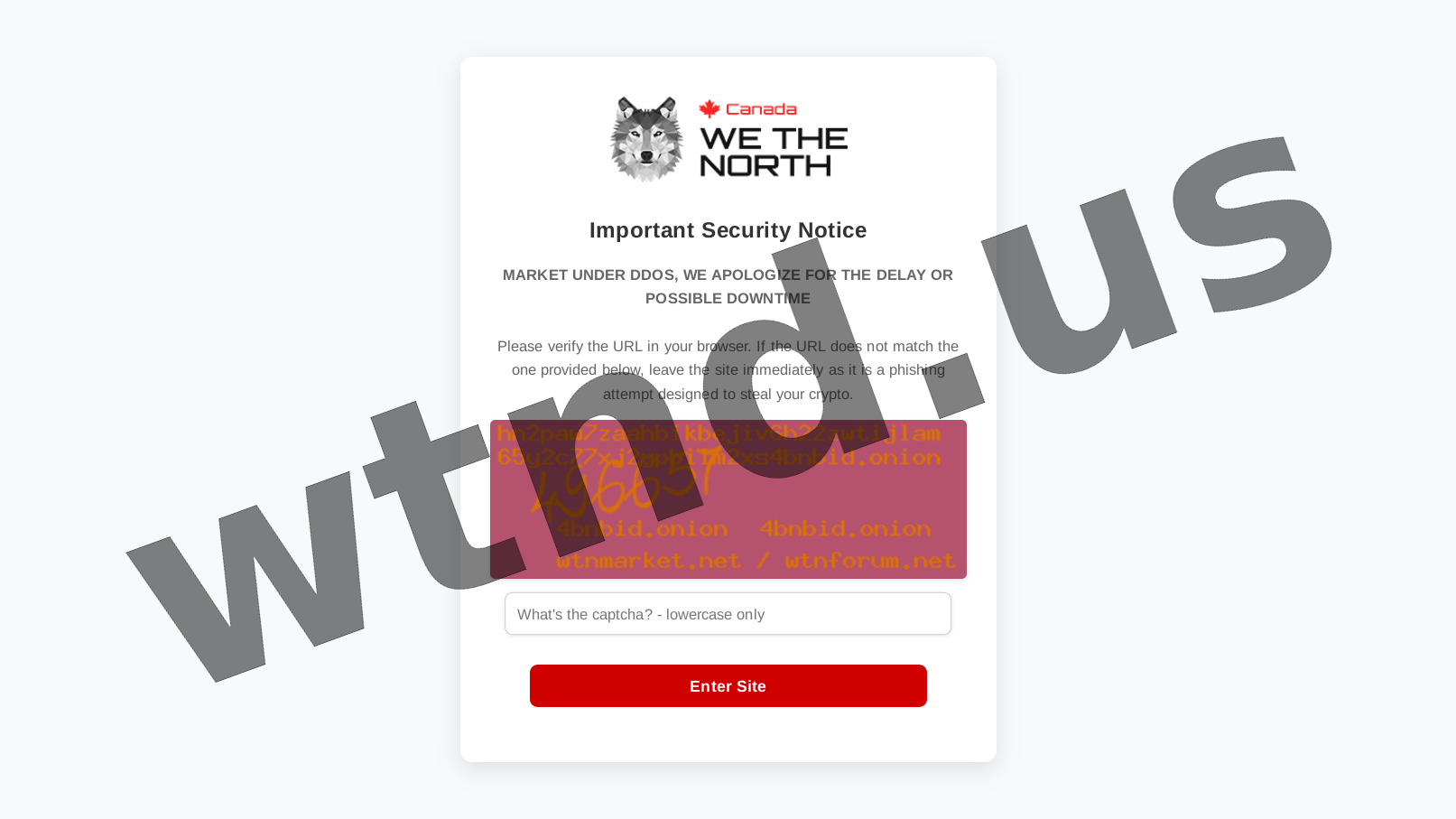
Fig 1. DDoS Protection Screen
Initial cryptographic challenge to filter automated scraping tools.

Fig 2. User Login Interface
Authentication portal featuring mandatory verification parameters.

Fig 3. Account Registration Page
Key generation and mnemonic phrase issuance module.
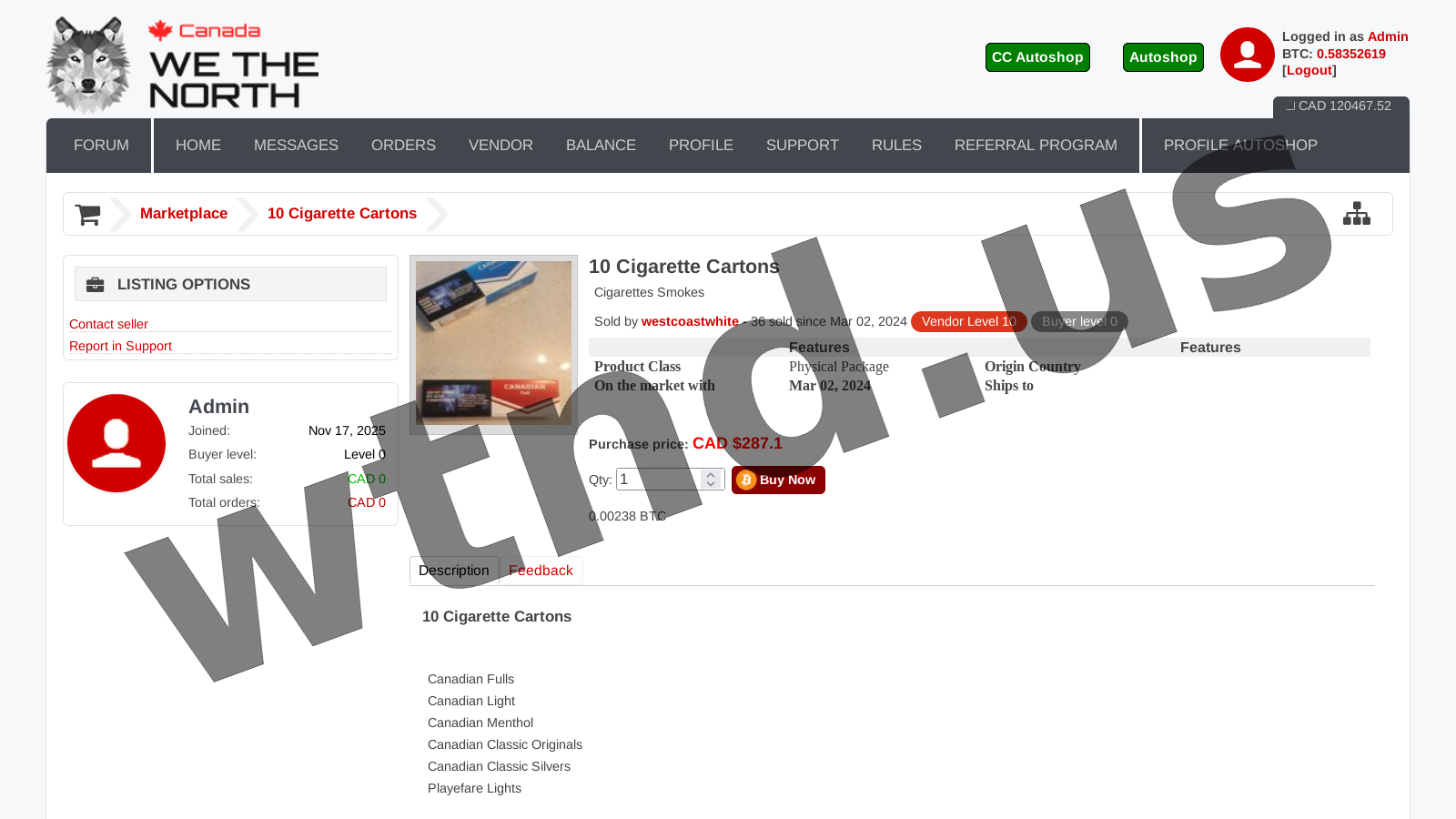
Fig 4. Main Market Dashboard
Categorized indexing of digital inventories and active listings.
Platform Statistics
While exact metrics remain obfuscated by design, independent scraping algorithms estimate a robust community framework stabilizing the ecosystem. The platform enforces strict protocols to ensure quality control and dispute resolution.
Note: Supplier verification requires a cryptographic bond deposit, mitigating malicious actors within the marketplace infrastructure. Recognized merchants from legacy markets can utilize signed PGP keys to bypass initial bond requirements, establishing trust continuity.